Types of Fraud in Remote Hiring
The field of cybersecurity started with the invention of computer networking. Those early security teams viewed threats from a network-centric perspective, and it took decades for the threat model to evolve. The first step was to shift from a strictly perimeter-focused approach into endpoint monitoring. With the adoption of cloud, infrastructure grew massively more distributed, and we began to adopt zero-trust architectures. But even in the zero-trust world, we still divide the universe into "insiders" and "outsiders," and we use separate systems of record for each class of user.
With the rapid advent of AI, we have arrived at a new moment: every system is under attack, from all directions, all the time, by everyone. The walls between physical security, cybersecurity, fraud, and identity must come down.
To grapple with Cloud, we abandoned the perimeter. To grapple with AI, we must abandon the User; our threat model must expand to encompass every stranger in the world, each of whom is a potential trust boundary. Once we accept that framing, we can start to see hiring fraud for what it actually is: not an edge case, but the first scaled exploit of a new structural vulnerability.
Recruiting Fraud vs. Hiring Fraud
Recruiting fraud and hiring fraud are related threats, but they work in opposite directions and affect different victims.
Recruiting fraud targets job seekers, with attackers posing as legitimate employers in order to extract fees, collect personal data, or deliver fraudulent check scams that can leave applicants out of pocket thousands of dollars before they realize what has happened. Hiring fraud runs in the opposite direction: the attacker poses as a legitimate candidate, gains employment, and collects a paycheck. They may or may not actually deliver much work, and they will certainly take advantage of opportunities to steal data as well. If they sense that they have been discovered, a ransomware attack may be their final gift.
A Glossary of Hiring Fraud
Resume fraud is the simplest form of hiring fraud, and one with which most organizations are already familiar. The spectrum ranges from simple "padding," through credential misrepresentation, to fabrication of entire roles and companies.
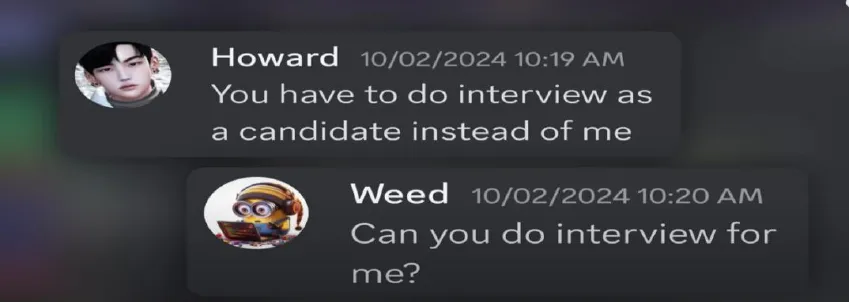
Proxy candidates involve a third party who assists during interviews or assessments, so that the person who passes the evaluation is not the person who shows up to do the work. The result is a bad hire whose actual skill set was never verified, generating wasted time, replacement costs, and operational disruption, but there is no obvious malicious intent, no data exfiltration, and no sanctions exposure.
Co-employment fraud extends further: a single worker holds multiple full-time positions simultaneously, routing deliverables to freelance contractors in other jurisdictions and sharing credentials across engagements. The harm is similar to, but much broader than, a bad hire, and includes legal exposure from violation of employment agreements, especially around data privacy, elevated risks from poor operational IT security, and the inevitable operational breakdowns from poor work product. The cost climbs, and the damage is harder to contain.
DPRK IT worker scheme involves state-sponsored North Korean operatives working in small teams with a mixed set of skills. These teams also usually include knowing or unknowing domestic collaborators, who may be providing the authorized legal identity for the worker. These attacks are far more effective than many other forms of hiring fraud due to the specialization of the team members: the person crafting false resumes and applying for the position, the person on the video call, the person or persons doing the work, and the person receiving payment are all different members of the team with specific competencies. A successful DPRK placement carries sanctions exposure, potential data loss, and costs that can reach tens of millions of dollars.
Tactics, Techniques, and Procedures (TTPs) Common in Hiring Fraud
The following TTPs have been documented by the FBI, DOJ, and the intelligence community primarily in the context of North Korean IT worker operations, but the techniques themselves are not exclusive to state-sponsored actors. As the tooling has become cheaper and more accessible, the same playbook has been adopted by individual fraudsters and organized criminal groups across multiple geographies.
Hybrid Credentials
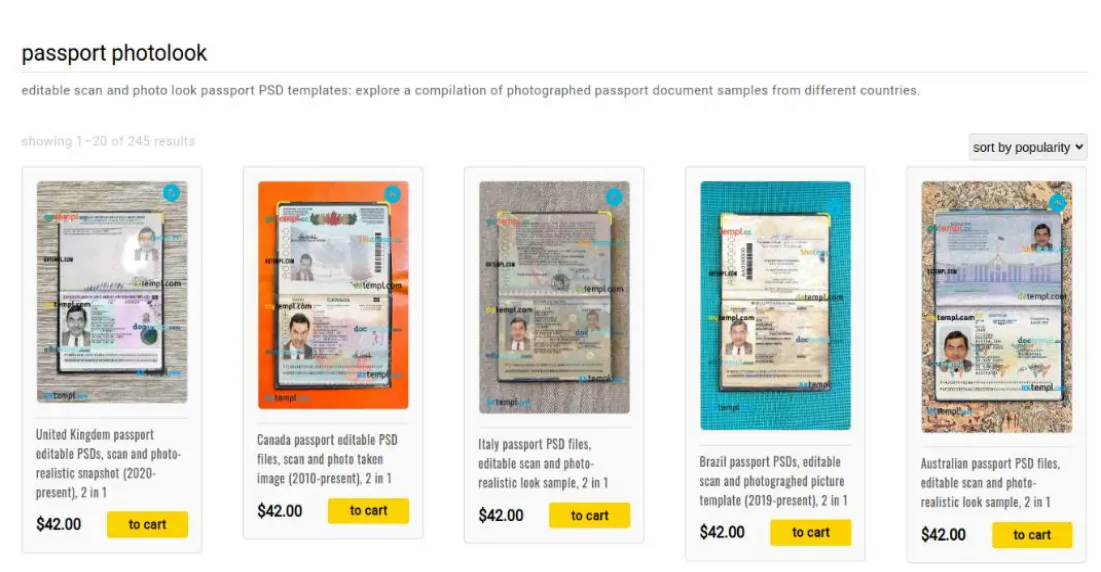
Hybrid credentials involve using a stolen or rented credential document, such as a driver's license, with a faceswapped photograph. These credentials may be used to assemble composite candidate profiles: a real name from one source, a fabricated or borrowed employment history, genuine professional certifications earned by a different person, and AI-generated portfolio content. SentinelOne tracked over 360 fake personas and more than 1,000 job applications linked to DPRK IT worker operations targeting their organization alone. The altered credentials may be submitted to both freelance work platforms and digital payment services, and will pass traditional identity verification checks.
Domestic Collaborators
The domestic collaborator, often called a "facilitator" in DOJ charging documents, is the human element that makes other common TTPs operationally viable. Synthetic credentials, network spoofing, and deepfake tooling all still depend on the ability to physically receive a laptop, cash a paycheck, open a bank account, or complete in-person onboarding and identity verification.
North Korean IT workers find non-North Korean nationals to serve as the nominal heads of regime-controlled front companies and hire third-party subcontractors to obscure identity. In prosecuted cases, domestic collaborators have included US citizens recruited through job postings, people already known to the operation, and in some cases individuals who were themselves deceived about what they were facilitating.
Facilitators have been convicted for roles in obviously criminal activities such as identity theft, as well as for running laptop farms or acting as proxy contractors in cases where they were not aware they were involved in criminal activity. The involvement of a domestic collaborator does not reduce the legal exposure for the companies targeted: hiring someone through a front company or paying wages that are ultimately transferred to a sanctioned entity can constitute a sanctions violation regardless of whether the employer knew what was happening.
Laptop Farms
Laptop farms are physical infrastructure operations designed to solve a specific problem: how does a worker physically located in one country receive and use company equipment that was shipped to an address in another country? A domestic accomplice accepts delivery of the company-issued hardware, connects it to the network, and provides remote access to the actual worker overseas, who then operates the machine as though they were local, with the company's endpoint management tools, VPN, and access controls all behaving normally from the employer's perspective.
The DOJ announced a nationwide crackdown in June 2025 on North Korean IT worker fraud, with enforcement actions spanning 16 states that included searches of 29 known or suspected laptop farms. In documented cases, individual laptop farm operators managed access for multiple remote workers simultaneously, functioning as a for-hire infrastructure service within the broader fraud ecosystem.
Location Spoofing
During the application process, fraudulent candidates may route their traffic through US-based VPNs or virtual private servers to ensure that IP geolocation checks return domestic results. Suspicious remote desktop use and VPN or VPS access should be treated as red flags during both account registration and active employment.
At the physical layer, the laptop farm addresses the problem that network spoofing cannot: a company-issued device that boots up and connects from overseas will generate geolocation metadata inconsistent with the employee's stated location. By routing activity through a domestic machine, the device's apparent location matches its shipping address. For contract engagements with clients who do not provide equipment, some operators use cloud-hosted virtual machines in US data centers.
Real-Time Video Deepfakes
Video interview fraud is the most visible of these techniques and has attracted the most public attention. Open-source models, especially those using avatar-based generation, are increasingly difficult to distinguish from real video and cannot be reliably detected by AI-based tools alone. However, real-time video deepfakes are rarely required; instead, attackers take advantage of faceswapping to create hybrid documents with their real face attached to a stolen name and identity, which allows them to attend interviews with no real-time deepfake needed.
Note on scope: These TTPs were documented in the context of DPRK revenue generation operations, but the techniques are not architecturally dependent on state backing. The same combination of synthetic credentials, remote infrastructure, and real-time impersonation is available to any sufficiently motivated actor. The DPRK cases are useful because they are well-documented and prosecuted at scale, and thus function as a reference implementation of what hiring fraud looks like when it is industrialized.
Assessing Risk Across Different Types of Hiring Fraud
The presence of lower-sophistication fraud in a hiring pipeline is not a separate problem from the DPRK risk. It is evidence that the structural gaps those schemes depend on are already wide open. If the gap is wide enough for a proxy candidate to clear a video interview undetected, it is wide enough for something far more consequential to pass through the same workflow.
Sources
Want to see Polyguard in action?
Experience real-time identity verification for your communication security.


